 By Aaron Strout and Joe Cascio
By Aaron Strout and Joe Cascio
Although experts in the social media space have been talking about how businesses might adopt microblogging tools like Twitter and Plurk, only recently have we started to see a series of new vendors cropping up in the enterprise microblogging space. This has been due in part to businesses needing to figure out how Twitter can benefit the enterprise. The fact that the mainstream press has started covering this topic has also helped to push things along (see Businessweek’s CEO Guide to Microblogging if you need proof).
Given the recent focus on business microblogging and the emergence of some new players like Yammer and Utterli (Formerly Utterz, Utterli has been around for a little over a year but just rebranded and is now becoming more enterprise-centric), it felt like as good a time as any to write a post about the business value of microsharing within the enterprise. Included in this post will be considerations for implementing microblogging and a few of the relevant players in the space.
Just to level set, it probably doesn’t hurt to define what microblogging is. For anyone that uses Twitter, Plurk, Identi.ca or any of the multiple other microblogging tools, microblogging is in some ways like instant messaging or text messaging but instead of it taking place one to one, it’s often one to many or many to many. I could take this entire post explaining what it is, but friend and Commoncraft founder, Lee LeFever, has done a fantastic job in his quick Twitter in Plain English video. I’d also like to clarify that this post is focused on businesses using microblogging within their organization vs. having a corporate presence in the public (like @comcastcares on Twitter). How corporations are using microblogging publicly is an equally relevant topic, however, numerous posts have already covered this phenomena.
Business Value
One of the lessons we learned from Web 1.0 (and the subsequent bubble) was the fact that startups that create technologies in search of a problem fail, even when VCs are stupid enough to throw wads of cash at them. This time around, most companies don’t get funded unless they are solving a business problem or at least offering up a technology that can enhance existing business processes. To that end, here are a few ways companies can tap into the power of microblogging:
Emergency Broadcast System: First and foremost, any company needs a way to reach all of its employees quickly and efficiently. E-mail is obviously one way to do this but increasingly, it’s hard to separate the wheat from the chaff. With many folks receiving hundreds of e-mails a day, it can take minutes if not hours before we get to an e-mail from the CEO.
Knowledge Management: Here’s where things get interesting. One of the biggest failings of many companies is the fact that they trap their intellectual property in Powerpoints, spreadsheets and Word documents and store them on shared drives and e-mail inboxes. Once the creator of that content walks out the door, the odds of their years of work finding its way into anyone else’s life are slim. As companies start uploading more and more content onto wikis, or central file repositories, these files can be linked to and indexed by conversational tools like microblogs.
Training: Any company that has gone on a hiring binge quickly realizes how painful it is to train new employees. If a formal training program exists, the materials are often outdated almost as soon as they are created. By identifying a few key influencers and allowing new employees to see their daily “streaming,†information and best practices can be shared more easily and in real time with little burden on the “trainer.â€
Expert Identification: Another area that many larger companies fall down is in making their resident experts easily findable. If you can see your company’s employees talking (possibly segmented by business unit or group within an organization), it wouldn’t take long to figure out who knows what about whom.
Seeing the Connectors: Good companies spend a lot of time on succession planning. Unfortunately, most companies don’t have a good handle on who the true connectors are within their organization. By analyzing conversations and watching the conversations of employees, senior managers can easily identify who these connectors are and then ensure these employees compensation and titles match their internal value AND start to add additional connectors if too much information is flowing through any one individual.
Inclusion of External Stakeholders: Back in the early 2000’s, extranets were all the rage. There would finally be a way for companies to include partners, investors and even certain customers in their daily conversations. Portals obviously began to fill this roll to a degree but none were ever truly conversational. Enter enterprise microblogging with the ability to include these aforementioned stakeholders in the mix.
Key Considerations
Enterprises considering microblogging as an internal function will have some common requirements. Here is our take on several areas that corporations tend to look at when they are considering a new technology:
Single Sign-On (SSO): A growing problem in the social media world right now is identity proliferation. With some notable exceptions that accept OpenID, most sites still require you to create yet another account in their system (or identity domain). In most enterprises, a fair amount of effort has already been expended on establishing single sign-on through the intranets’ LDAP registry. It would be highly desirable to leverage this capability to enroll employees in the microblogging system. So, an enterprise microblogging solution must have flexibility in adapting to existing ID and sign-on registries.
Reliability: Initially, microblogging may seem like a non-essential, nice-to-have kind of tool, but our bet is that most businesses will find it very quickly becomes indispensable for keeping important lines of communication open. People, on their own, will invent many different uses for such a simple tool, as they have with Twitter. In a large corporation with geographically distributed sites, it would be best to have a solution that allows each campus to run its own server and not be dependent on a remote centralized service. These distributed servers would exchange data to unify the system as a whole. See Distribution below.
Analytics: Businesses will eventually want to analyze the traffic on their microblogging sites. They’ll want to know who follows who, who posts the most and to who and most importantly, a feature I’d love to have in Twitter, the ability to see and search all my posts and other posts selectively for important information, just like we can search our G-mail accounts now.
Security:This will probably be of paramount concern at least initially in most businesses. Most corporations are very aware of keeping internal communications safe from prying outside eyes. An enterprise microblogging solution must provide for fine-grained authorization and trustworthy security of communications. Management, through the IT department will want to be able to restrict who can see certain posts.
Scalability: The word Enterprise covers a huge spectrum of organizations. An enterprise microblogging solution should be scalable from less than 100 users to tens or even hundreds of thousands of users, spread across the globe. The ability to distribute and federate many local servers on the corporate intranet will help to satisfy this need.
Groups: Enterprises comprise many different groups within their walls. Not just departments, but project teams, ad hoc working groups, common interests, etc. An enterprise microblogging solution must provide for the easy definition of groups or tags, where any employee user can belong to many groups.
Distribution: This requirement has been touched on already, but it should be mentioned again because of its importance to other requirements. It refers to the ability of the enterprise microblogging solution to be decentralized, spread out across wide geographic areas, and hence to become fault tolerant, so the failure of any one node does not cause a failure of the whole system.
Interoperability: Clearly a distributable enterprise microblogging solution would require its various nodes to federate and interoperate, but a corporation wishing to allow interaction with its customer base outside its walls would require a solution that interoperates with other microblogging solutions that may exist, yet allows only some posts to be seen outside the corporate firewall.
Current Players
Until recently, most vendors in the community or social media space have either focused on delivering microblogging tools to the public while software providers that focused on the enterprise tools busied themselves with delivering better wikis and other collaboration tools. Not anymore. A slew of startups (and one or two more tenured companies) have now turned their attention to the less sexy but immediately more profitable enterprise microblogging space. Below you will find a list of some of the major players in this space along with a quick description, pros and cons of each. If we’ve missed a player, please feel free to add to the comments and we’ll strongly consider adding them into this post:

Yammer (from TradeVibes) Yammer is a tool for making companies and organizations more productive through the exchange of short frequent answers to one simple question: “What are you working on?â€
PROS: Easy to turn on and screens out folks outside of the corporate domain. These guys have obviously learned a thing or two from where some of the existing microblogging tools fall down.
CONS: No single sign-on functionality (at least not that we could see). Tricky to add other “partners/contractors†that don’t have e-mail addresses matching the corporate domain. Hosted by outside company, can’t be deployed inside the firewall.

Laconi.ca (from Wikipedia) An open source microblogging tool written in PHP that implements the OpenMicroBlogging standard. Laconica was created as an open source, distributed alternative to Twitter, and was originally used by the identi.ca microblogging service.
PROS: Built on opensource software so it’s completely customizable. It also integrates with well-known Twitter client, Twhirl giving power users the ability to manage external and internal facing microblogging activity in a seemless fashion. It is based on the Open Microblogging protocol specification, so other implementations are possible.
CONS: As is the case with any opensource application, its greatest asset (flexibility) is also its biggest weakness (not super user-friendly out of the box). Scaling, federation and interoperation have yet to be seriously tested.

Utterli (from Utterli.com) Utterli helps you create and follow discussions with friends or new people with similar interests. You can create or join a discussion from any mobile phone or computer. Utters are cool because they can be audio, video, pictures and text, and it’s really easy to post to your other online profile pages.
PROS: Utterli’s two biggest strengths are easily its multi-media and mobile capabilities. It’s fairly easy to create a “group†on the fly and coming soon will be enterprise-friendly SSO and security capabilities. Stay tuned for more on this front.
CONS: The least “Twitter-like†out of any of the existing enterprise microbloggers. We’re not completely sure that’s actually a weakness.
Existing enterprise players like Jive , Awareness , Mzinga * and Drupal
PROS: These guys are in the business of working with enterprises and catering to their needs. Don’t be surprised to see some of these players (if they aren’t thinking about it already) jump into this game in the next 3-6 months. If and when they do, they will be forces to be reckoned with.
CONS: While none of the existing community providers are actively touting an enterprise microblogging tool, it wouldn’t be a stretch for any of them to create one based on existing tools. The fact that they haven’t created one yet does put them at a slight disadvantage on the learning curve.
Will They or Won’t They
As the corporate adoption of microblogging tools like Twitter continues to increase, it’s only a matter of time before companies decide that there is something there worth exploring. Well-known startups like Mahalo have a 50% adoption rate of Yammer. Companies like IBM are using similar functionality on their Facebook-like internal communities. With so many potential benefits, why wouldn’t a company want to give this a try?
About the authors:
AARON: As Vice President of Social Media at Mzinga, Aaron Strout focuses on creating business value for Mzinga through viral marketing channels, including blogs, podcasts, twitter, and speaking engagements.
JOE: Joe Cascio is an independent software developer turned “social media enthusiast.†Joe is also the chief developer of an experimental social media identity site called SociaLogic.org. His “biggest†current interest, however, is Distributed Microblogging (i.e., Twitter). Joe maintains a blog as JoeCascio.net and you can follow him on Twitter here.
*In full disclosure, I work for Mzinga as the VP of Social Media.
---
Related Articles at Mashable | All That's New on the Web:
Mashable Readers: 20% Off Enterprise Mashups Event
Pownce: Publicly Share Files via Lifestreams (Why Not?)
Call for Video Submissions for Enterprise 2.0 LaunchPad - Deadline is Tomorrow!
Google Earth Enterprise Version Update Released
Enterprise Microsharing Matrix: Yammer and 14 Rivals Compared
Seesmic Acquires Twhirl, for Desktop Video Microblogging
The Daily Poll: Google Apps Enterprise


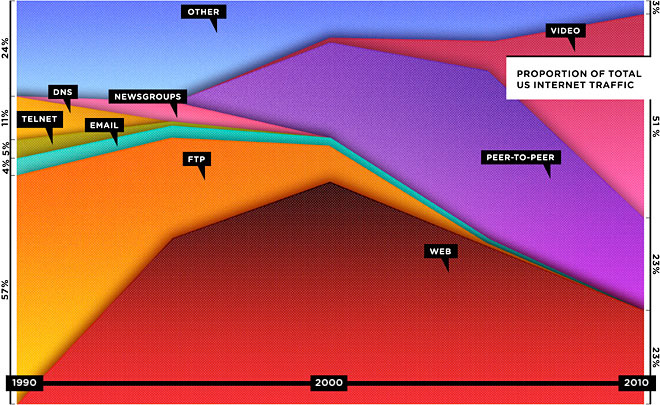 Their feature, The Web is Dead. Long Live the Internet, is live at Wired's own website.
Without commenting on the article's argument, I nonetheless found this graph immediately suspect, because it doesn't account for the increase in internet traffic over the same period. The use of proportion of the total as the vertical axis instead of the actual total is a interesting editorial choice.
Their feature, The Web is Dead. Long Live the Internet, is live at Wired's own website.
Without commenting on the article's argument, I nonetheless found this graph immediately suspect, because it doesn't account for the increase in internet traffic over the same period. The use of proportion of the total as the vertical axis instead of the actual total is a interesting editorial choice.







 Anyone who has pried opinions out of me (or seen my eyes glaze over) knows that I admire simple, clear language and despise buzzwords and jargon. Well, at a recent
Anyone who has pried opinions out of me (or seen my eyes glaze over) knows that I admire simple, clear language and despise buzzwords and jargon. Well, at a recent  I don’t know how accurate it is to say Senator Barack Obama is a Mac to Senator John McCain’s PC, but those convinced of this premise will either delight in or scorn the fact that the Obama for America campaign has presented a
I don’t know how accurate it is to say Senator Barack Obama is a Mac to Senator John McCain’s PC, but those convinced of this premise will either delight in or scorn the fact that the Obama for America campaign has presented a 
 Recently I had the chance to attend an event called
Recently I had the chance to attend an event called 








 By Aaron Strout and Joe Cascio
By Aaron Strout and Joe Cascio 





